Enterprise security in the browser.
Year-long development on a privately-distributed browser extension that scans webpages and files for credential-phishing and unsafe content. Distributed through a CMS portal with organisation-specific branding, never listed on public web stores.
Enterprise security without a public footprint.
An agency client serving large enterprise customers needed a browser extension that stops credential phishing and unsafe downloads on the open web — but they could not ship to the Chrome Web Store. Their customers require unlisted, locally-installed software with per-organisation branding and licensing.
The extension had to behave like a polished consumer product when an end user opened it, while every flow — activation, support, branding, file-scan toggles — was driven by configuration the agency’s CMS pushed down. Customisable from the back end. Invisible from the public store.
A configurable extension, every surface skinnable.
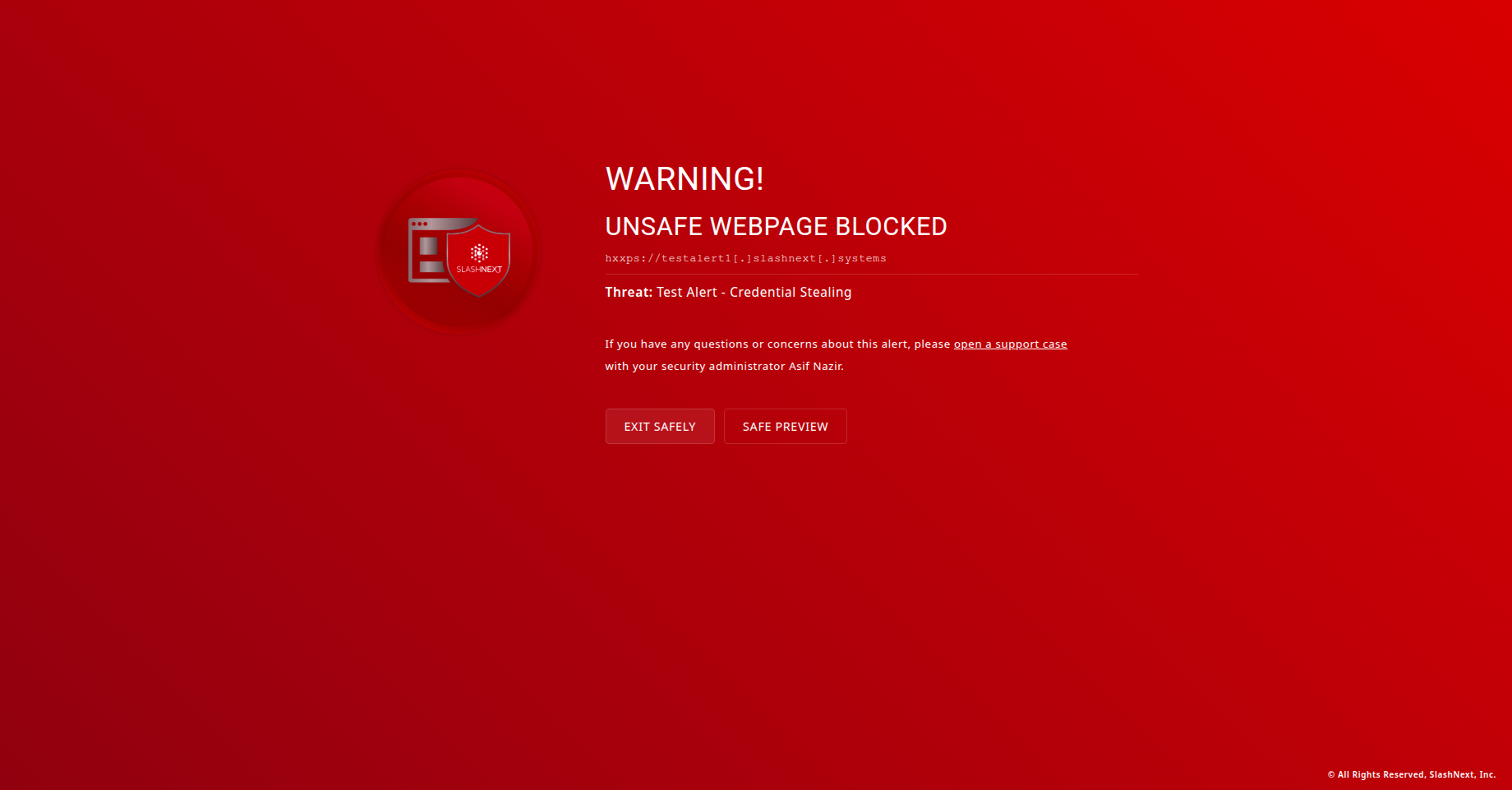
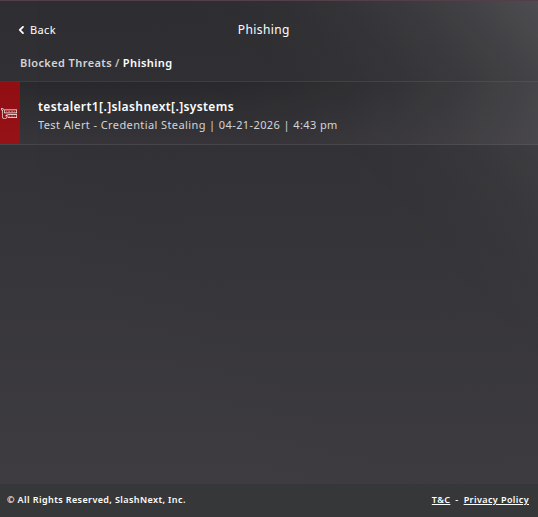
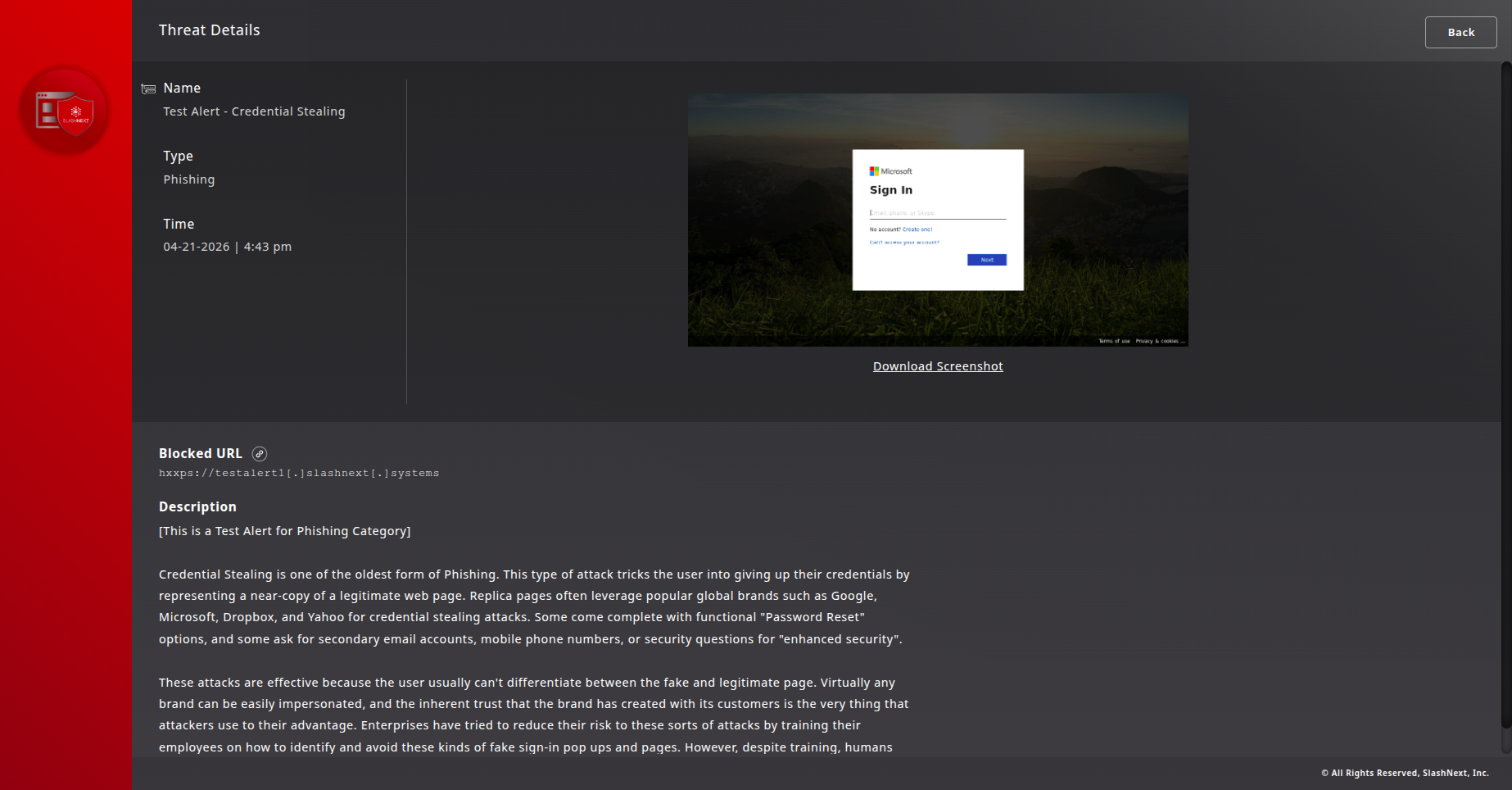
Manifest V3 extension with twenty-plus screens covering the full lifecycle: activation by email or key, error states for invalid or missing keys, dashboard popup with threats blocked and pages scanned, threat-list drill-down, in-browser warning takeovers when an unsafe page loads, safe-preview escape hatch, file-scan opt-in, support and feedback flows.
Every brand element — logo, colour, copy — flows from the CMS at install time. A single codebase ships to multiple enterprise tenants with their own visual identity. The extension itself never touches a public store; the local installer is part of the deliverable.
A year-plus engagement, one developer, steady ship.
We embedded with the agency for over a year, owning the extension surface while their team owned brand, CMS, and customer relationships. Twenty-plus screens shipped iteratively, with every state — happy path, error, edge case — designed and built end to end. The product is in active production with the agency’s enterprise customers.